# Lab - AAA (IOS-XR)
Load the MDT topology:
```
containerlab destroy -a
containerlab deploy -t mdt/mdt.clab.yml --reconfigure
```
Configure AAA on XR1 using the following guidelines:
* Configure a RADIUS server at 155.1.1.1 using port 1812 for authentication, port 1813 for accounting, and CISCO123 for the key. Use a timeout of 3 seconds.
* If the RADIUS server is not available, fallback to local passwords for authentication.
* Create a user name ADMIN with password CISCO123 with root-lr priviledge
* Create a user name NOC with password CISCO123 that has access to read the RIB, OSPF, and interfaces.
* Use the RADIUS server for accounting for each SSH session that is started.
* Do not require any authorization, as RADIUS or the user database will provide authorization during the authentication process.
* Enable SSH for the default VRF.
* Allow SSH for up to 50 simultaneous sessions.
## Answer
```
#XR1
radius-server host 155.1.1.1 auth-port 1812 acct-port 1813
key CISCO123
timeout 3
!
aaa group server radius RAD_GROUP
server 155.1.1.1 auth-port 1812 acct-port 1813
!
username ADMIN
group root-lr
password CISCO123
!
taskgroup NOC_TASKS
task read rib
task read ospf
task read interface
!
usergroup NOC_GROUP
taskgroup NOC_TASKS
!
username NOC
group NOC_GROUP
password CISCO123
!
!
aaa accounting exec VTY start-stop group RAD_GROUP
aaa authorization exec VTY none
aaa authentication login VTY group RAD_GROUP local
!
line template VTY
accounting exec VTY
authorization exec VTY
login authentication VTY
!
vty-pool default 0 50 line-template VTY
!
ssh server session-limit 50
ssh server vrf default
```
## Explanation
This lab is fairly straight-forward. We configure a RADIUS server, assign it to a group, and use it for AAA. Just like with IOS-XE, the first method in the list is tried first, and if it fails to return a reply, subsequent methods are attempted.
We create a task group with the granular permissions we are permitting to NOC users, assign this to a user group, and assign the user group to the NOC user.
The method of applying the AAA lists to the VTY lines is different on IOS-XR. We must apply it to a template, and then apply this template to the VTY-pool.
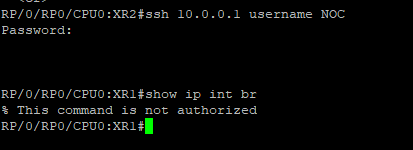
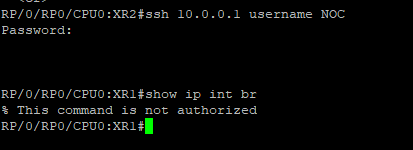
If we SSH from XR2 to XR1 with the user NOC, we can see that many commands are not authorized. Even though we are using **authorization none**, the authorization comes from the authentication process.
In config mode we do not have the ability to actually set anything:
```
RP/0/RP0/CPU0:XR1(config)#?
abort Abort this configuration session
alias Create an alias for entity
clear Clear the uncommitted configuration
commit Commit the configuration changes via pseudo-atomic operation
describe Describe a command without taking real actions
do Run an exec command
end Exit from configure mode
exclude-item Negate a command or set its defaults
exit Exit from configure mode
ip Deprecated, use ipv4 instead
no Negate a command or set its defaults
root Exit to the global configuration mode
service Modify use of network based services
show Show contents of configuration
```